I just finished up being a juror on a weeks long felony criminal case. A good hunk of the case depended on some video evidence from commercial outdoor security cameras in the middle of the day. I was in utter disbelief at how potato quality the video was, how it was mishandled, and the prosecutor wants us to reach beyond a reasonable doubt on some blocky squares that might be somebody’s arm? or leg?
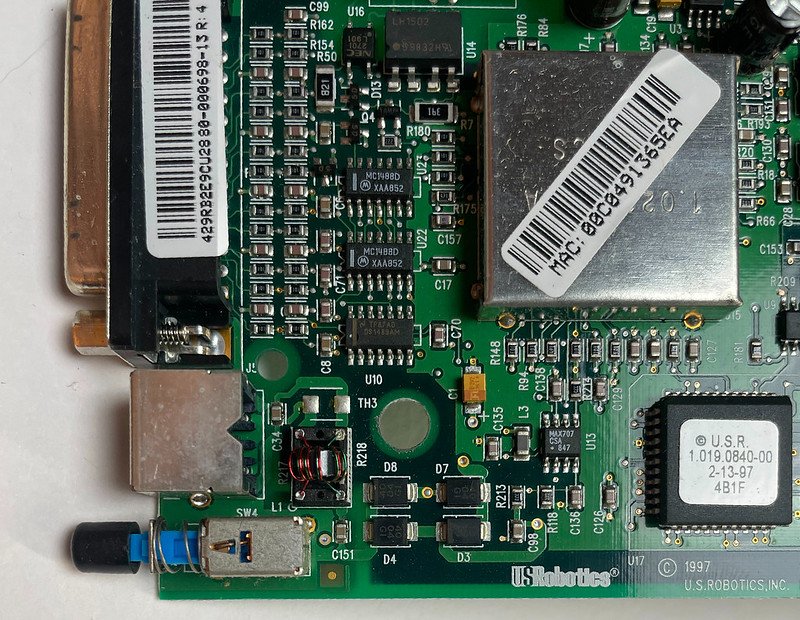
After dealing with people breaking into my dad’s hardware store over the years and using those experiences to constantly refine how I capture video footage to better identify individuals to the sheriff, I have ✨Lots of Opinions✨ about security surveillance video. Video quality has gotten amazing over the last 10 years, going from shitty analog cameras to shitty 640 x 480 motion JPEG cameras, to 1.3 megapixel CCD/CMOS sensor cameras with audio, and now we’re up up to 8 megapixel 4K cameras that capture blades of grass and audio 20 feet away for $99. I am constantly swapping out cameras over time as things get better and what used to be blurry blobs at night are turning into real features. Beyond higher resolutions I’ve always advocated for better framing, lower camera positioning, just like you would taking a photograph. It always makes me sad when I see footage from high up of the top of somebody’s head and can’t tell anything other than their clothing.
To be fair in this case most of the crime was obscured on the other side of a vehicle so even a 4K video wouldn’t have helped much.
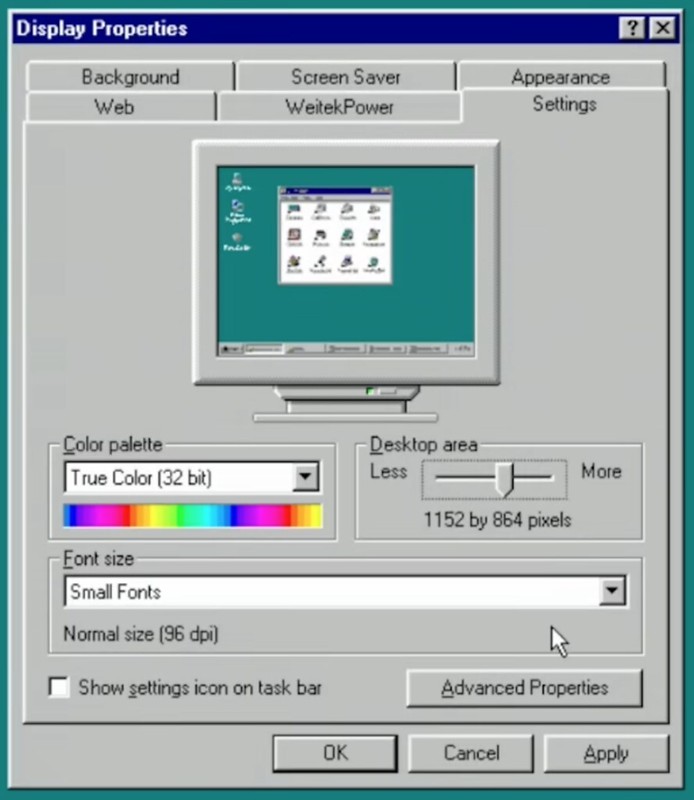
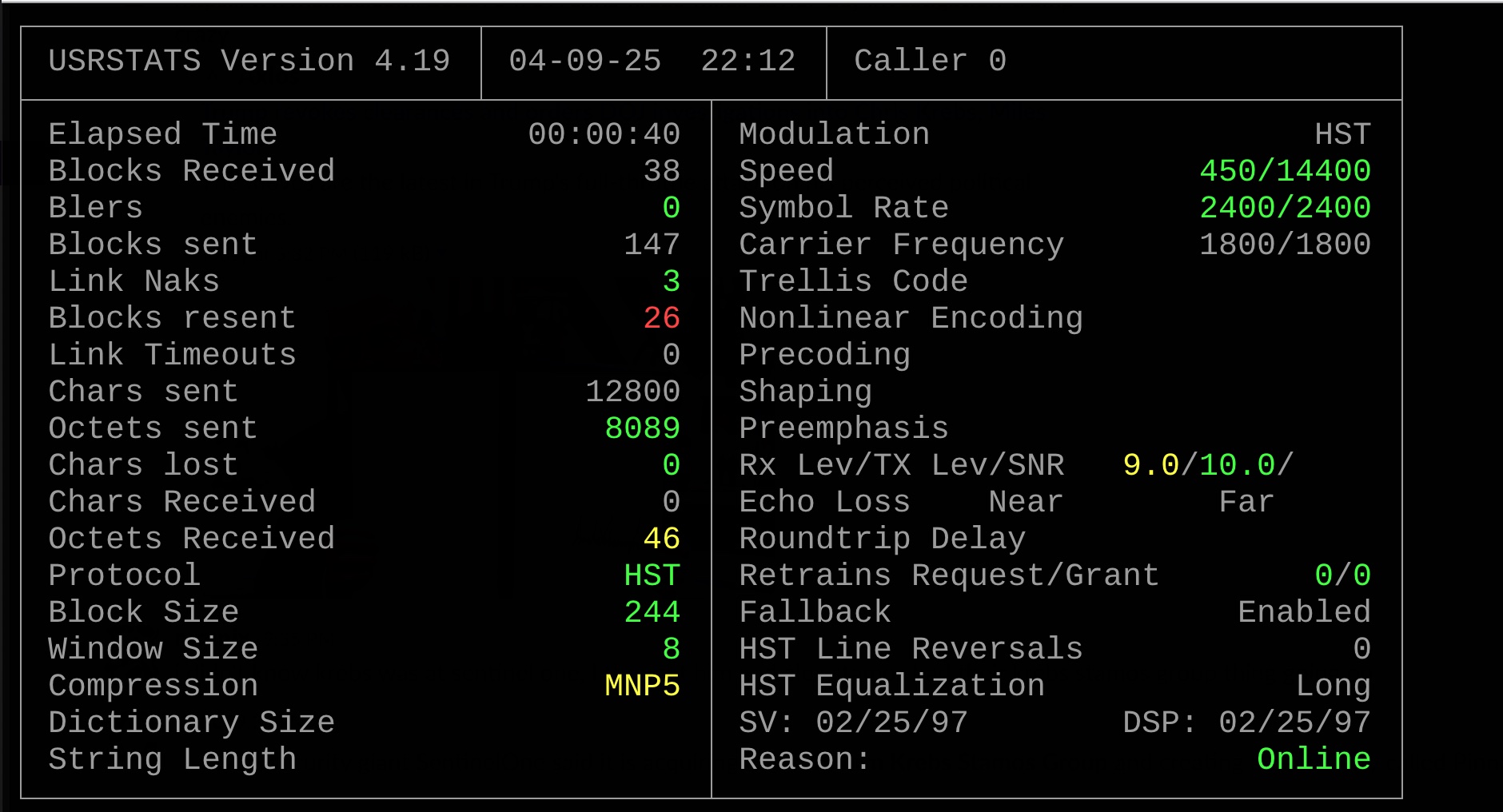
First off, the owner of the video system provided to the cops a screen recording of their security DVR system while it was up displaying 11 cameras angles at once, that was it. They testified while the cameras recorded independently they could not provide any source video files because “our system won’t do it, they’re so huge, it will break”. I have no idea what the cameras were but I imagine on a commercial system it was probably a few megapixels each. Because it was a recording of a recording, all those pixels and detail, just utterly thrown away and gone. And because it was an overview screen, all video windows were 1/11th the size of the total screen. What might have been 2560 pixels wide originally might now be 480 pixels wide on screen.
Now imagine this being played for a jury on a 53″ TV on a wall 20 feet away, we can’t see shit for details or people. During jury deliberation we got to view the video all we wanted on a old Thinkpad on the jury room, but still pretty bad. I’m not so sure if this was an improvement over just a cell phone recording of a monitor. Also interesting, the jury room laptop has to be old enough to play CD-ROMs.
Based on differing testimony between the video owner and the detective who collected the video, and general prickliness about the situation, I got the distinct impression the owner did not want to help the police at all due to their personal feelings/politics. Even with a violent crime happening on their property, they just wanted to do the bare minimum. They couldn’t be bothered to even get a screen recording of the individual camera views. The video file provided was panned/zoomed in a lot on the 11 camera view to follow single camera views as the action unfolded and moved around, and sped up/slowed down quite a bit presumably to get past times when not much was happening. It’s not clear who did the editing. The owner claimed the detective directed them (or their staff) how to do the screen recording, the detective claimed the owner just gave him a chair and a computer and left him figure it out on his own.
There was also the issue of video retention. The system owner said their system strictly captured 10 days and deleted everything, with no way to save files, which seems dubious to me. The detective admitted on the stand he had made a mistake at handling the video, he didn’t get around to reviewing the footage he was given until several days later due to workload. By then he realized there were no single-camera views on his USB drive, just this aggregate view, and by then all the original footage was all gone.
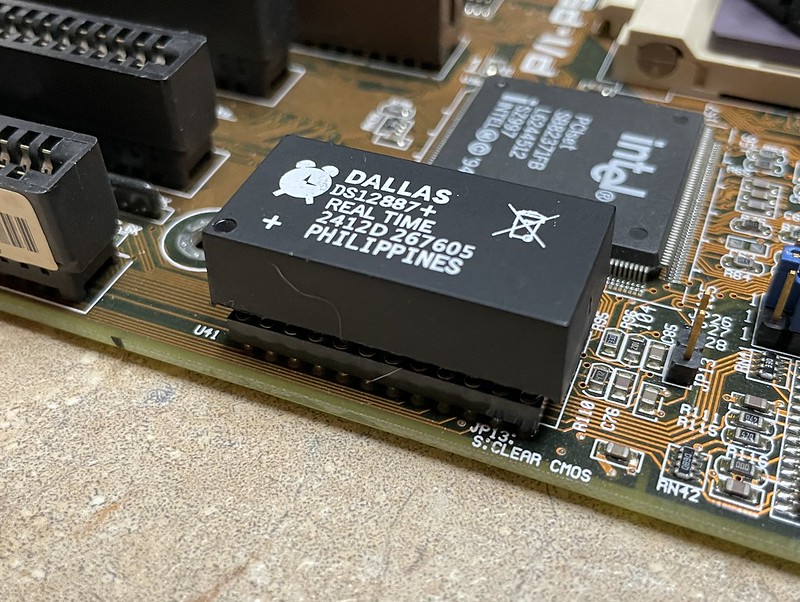
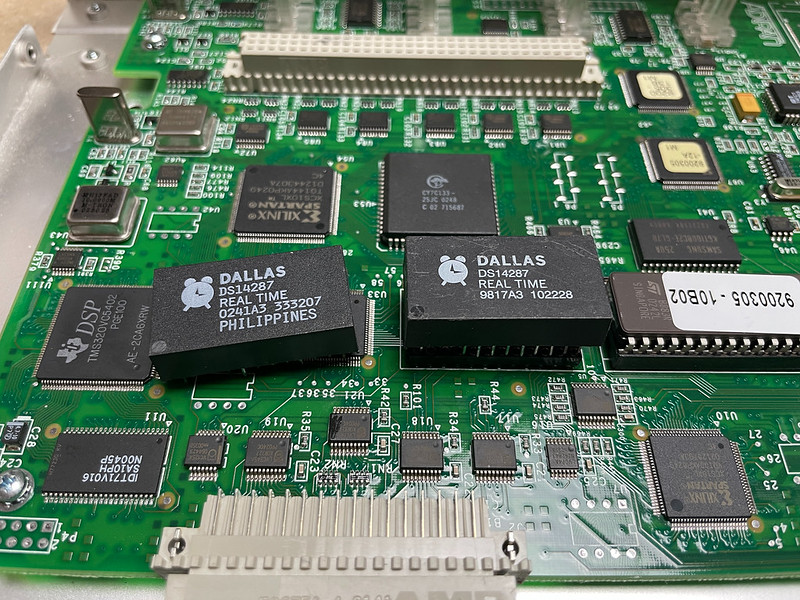
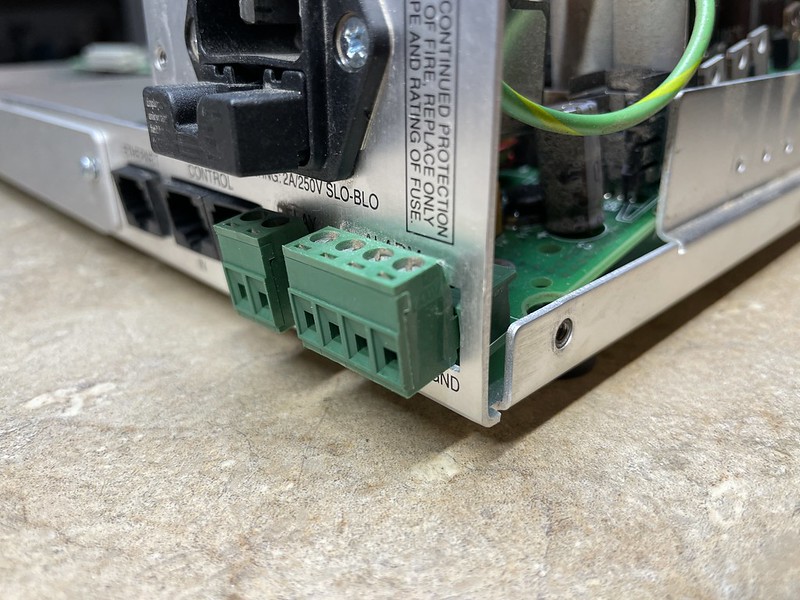
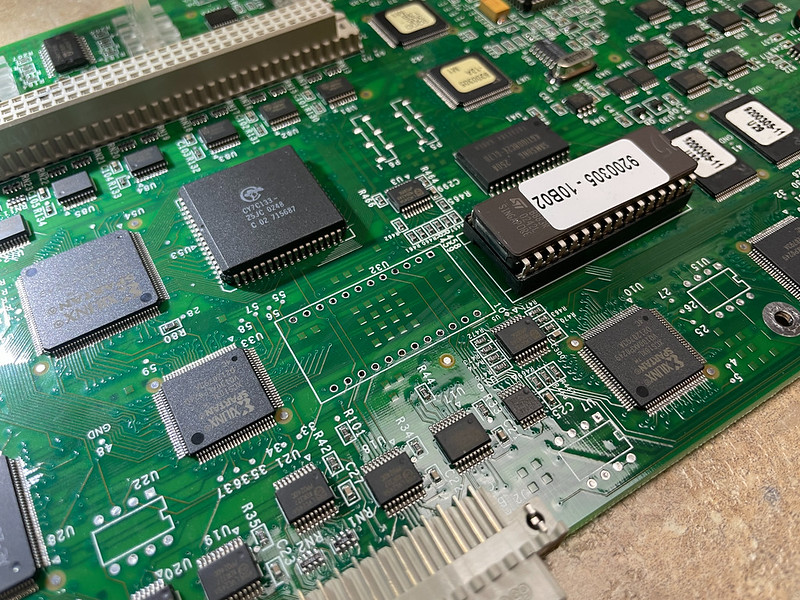
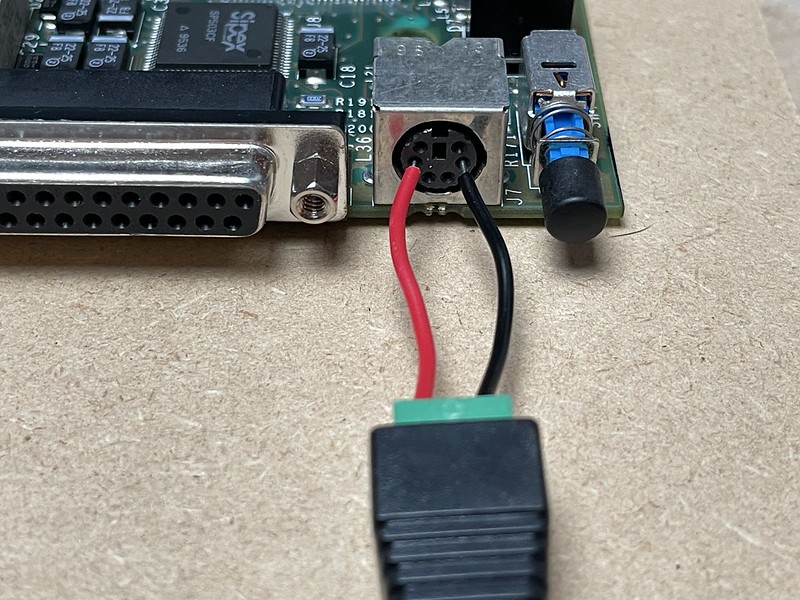
I get that the owner might not be a computer person, they’re at the whim of a black box they bought, maybe going by what somebody else told them about the system, and this whole ordeal is taking time out of their day, but still what kind of shitty system was this that it fails at its only job unless it was just to check off a box for insurance or corporate policy.
The original speeding up/slowing down of the video was problematic too. If it was sped up the person looks like they could be running away to flee, whereas normal speed they look like they’re calmly walking. The prosecutor had a video expert try to re-create the original timeline by making the frame rate uniform, and upscale the video to make it larger which helped but it made for jerky, blocky video.
I later told this story to a cop friend who did detective work and he just shook his head. He told me that in a situation like this where the owner couldn’t/wouldn’t provide original footage, especially if the victim was hurt, he “would get a search warrant in a heartbeat, take the system, the hard drives, everything, and get their own people to get that evidence”.
So I guess the lesson of the story is, if you want to use your video footage to prosecute theft, crimes, or whatever on your property make it easier on everyone by providing the best, largest, footage you can as quick as you can, and hang onto the original files. Imagine twelve people trying to look at it from across the room. Not so much tiny windows on a screen. Also maybe not store your video footage on your only NAS in case it gets taken. Much like how I say what you say can wind up in double-spaced transcript in court, be mindful of how your footage plays out for a jury, literally.